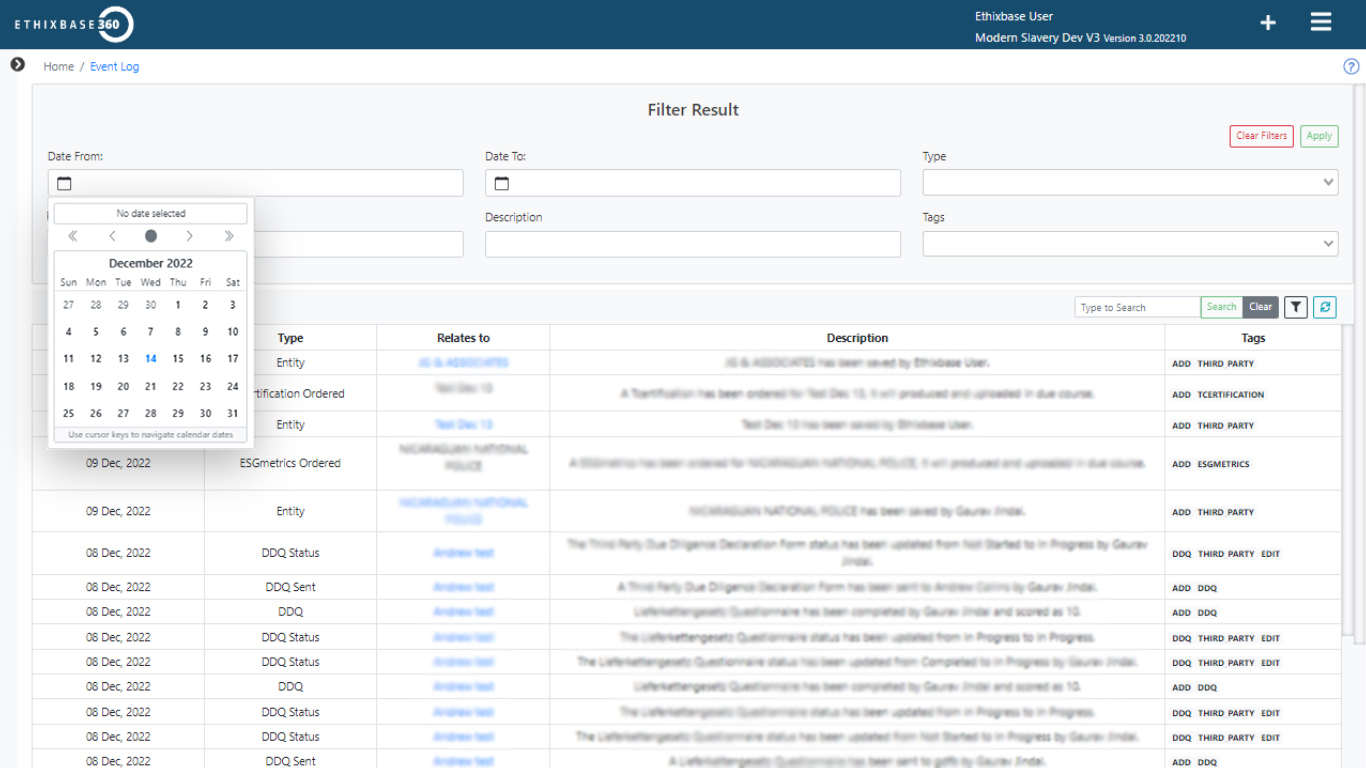
Configure workflows and automate risk-based actions
Ensure a consistent, automated and risk-based approach configured to your businesses third-party risk management processes and policies.
Workflows & Case Management
Ethixbase360’s configurable technology allows you to automate your third-party risk management workflows based on existing processes, with the ability to scale, refine and evolve as your business grows in size and complexity. Workflows can be configured to automatically detect specific events, risk levels and types and to trigger proportionate responses throughout the third-party risk management lifecycle.
Additionally, case management allows for human interactions in workflows, escalating third parties who require decisions and next steps to pre-defined ownership hierarchies while tracking open tasks through to completion. All tracked to evidence compliance.
Remove manual processes and streamline onboarding and ongoing third-party risk management
- Create business specific attributes to calculate and determine risk.
- Automate actions based on levels and types risk posed such as risk proportionate due diligence or triggering risk specific third-party engagement strategies such as questionnaires or training.
- Automatically extract information from returned due diligence measures to append third party profiles and, should risk change, trigger proportionate review.
- Set manual intervention points in workflows to facilitate decision making and create and assign tasks to track through to completion.
- Set policies to refresh compliance measures on third parties based on anniversary dates or influenced by risk level or type.
- Be confident that workflows are being consistently and automatically applied, saving your team time and providing a fully documented third- party risk management program.
Ready to get started?
Resources
Our Latest News, Case Studies, Webinars & More
A Practical Guide to Third-Party Cyber Risk Management
Cyber risk is no longer contained within your organisation. Today’s most damaging breaches don’t start with you, they start with the third parties you rely on. [...]
Compliance Implications of Anthropic’s Dispute with the Pentagon
In late February 2026, the US Department of Defense (DoD) designated the artificial intelligence (AI) company Anthropic a supply chain risk, a first for a US company. [...]
Human Rights Due Diligence and Modern Slavery: Global Expectations for Compliance Programs
Human rights and modern slavery risks are receiving heightened regulatory and enforcement attention across global supply chains.[...]
Key Takeaways from our Webinar: Managing Human Rights and Corruption Risks Across Life Sciences Third Parties
Key Takeaways from our Webinar: Managing Human Rights and Corruption Risks Across Life Sciences Third Parties In Partnership with Ethics and Compliance Switzerland. [...]
Anti-Corruption, Fraud & Global Compliance For Life Sciences
We’re proud to sponsor 21st Annual Anti-Corruption, Fraud & Global Compliance for Life Sciences conference on May 5–6, 2026! They’ll be sharing how Ethixbase360 supports life sciences companies[...]