Ethixbase360 Cyber TPRM Platform, powered by S-RM
Third-party cyber risk has become one of the most significant and least understood threats facing modern organizations. The world of work has changed and so has the behaviour of cyber criminals.
Third-party cyber risk demands stronger oversight, shared visibility and accountability across business units to identify risks before they become breaches.
Why are third-party cyber-attacks attractive to criminals?
One breach,
many victims
Compromise a single third-party get access to hundreds of organizations.
High return
on effort
Attackers invest effort once instead of repeating attacks organization by organization.
Attackers have
more leverage
Widespread operational impact increases pressure to pay, respond quickly, or negotiate
Why do third-party cyber-attacks succeed?
Limited Visibility of
Third-Party Ecosystems
Many organizations will tend to focus on their ‘critical’ vendors due to limited resources
Unclear Accountability
& Ownership
No single team owns third-party cyber risk end-to-end
Organizations
are underprepared
Vendor assessments often stop at onboarding – leaving a major blind spot.
We created TPRM Cyber to respond
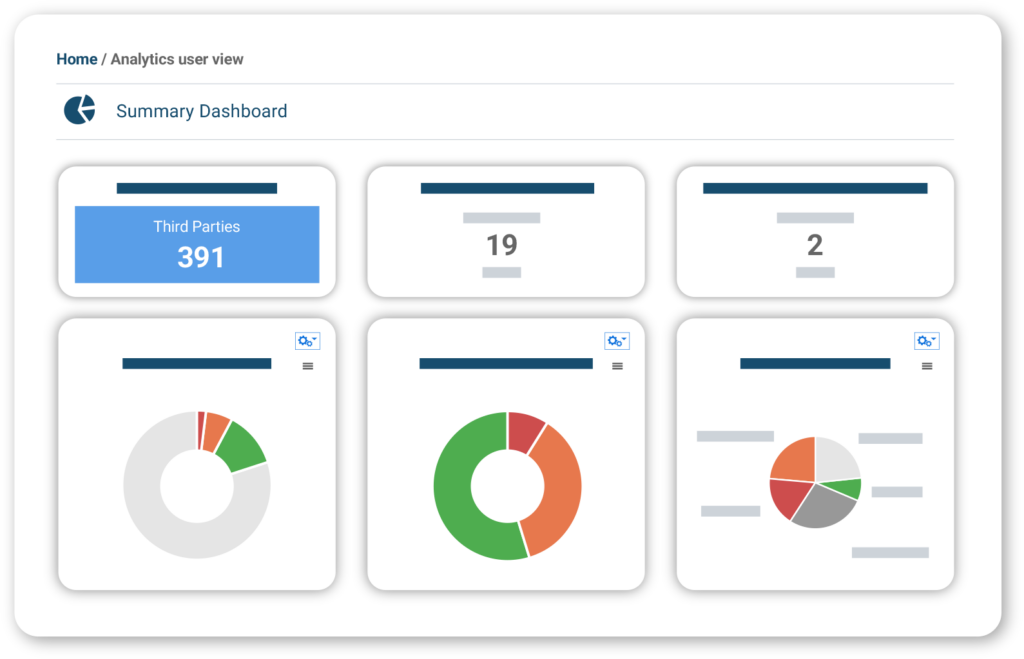
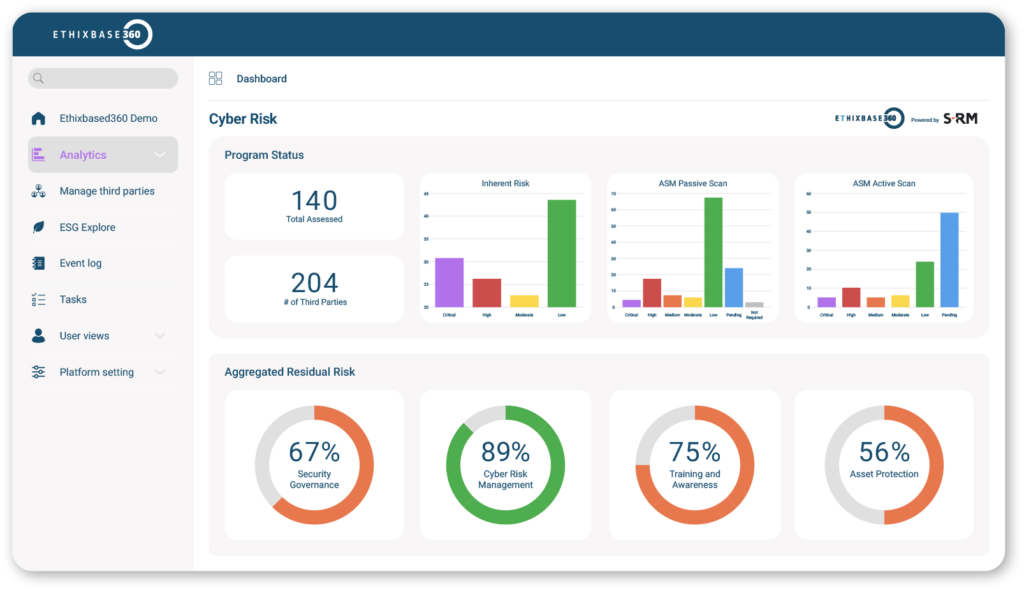
Unify your approach to third party cyber risk
Structured workflows and real-time insights help teams identify, investigate and remediate threats quickly.Visibility across third parties
Our platform keeps you ahead of the game, helping you assess and prioritize every vendor, not just the critical ones. So, you know where real risk is and act quickly.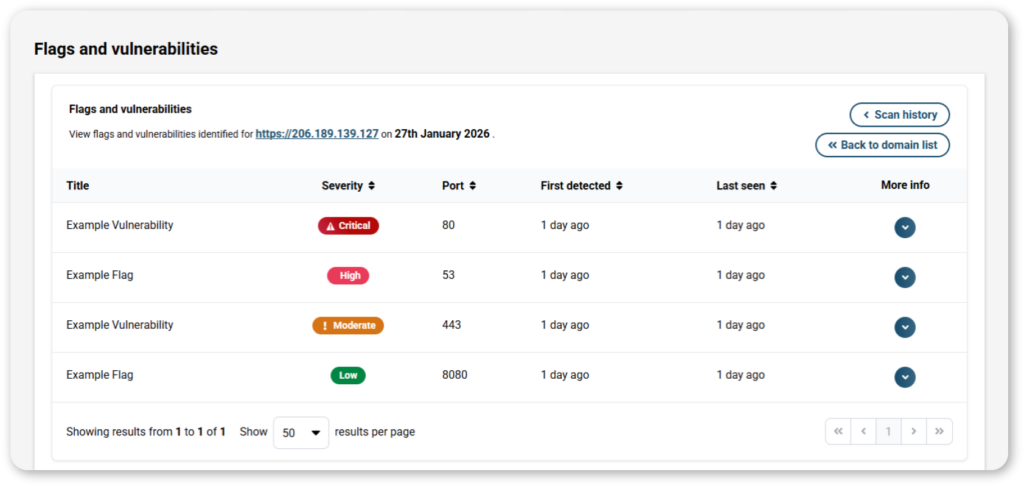

Expert backed by SR-M
Our partnership with SR-M, a global leader in cyber incident response and advisory, allows us to respond quickly to escalated cyber risks, ensuring not just visibility, but resilience.A Platform built around your organization
Configure tailored workflows, assessments and automations that integrate cyber alongside other vendor risk domains at the scale your organization needs.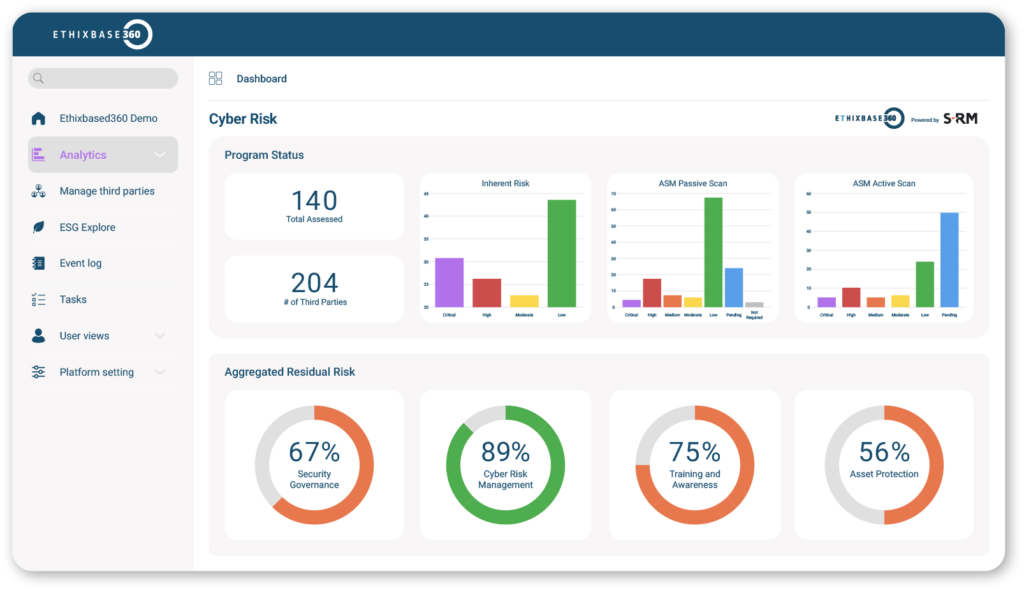
Frequently Asked Questions
How is third‑party cyber different?
How is third‑party cyber different?
Who owns cyber risk internally?
Who owns cyber risk internally?
Ownership of third‑party cyber risk is typically shared across risk, security, and compliance teams. Effective management requires collaboration between these functions to ensure visibility, accountability, and response.